The ubiquity of IoT has revolutionized every sector. In healthcare, IoT has provided critical real-time insights for patients and practitioners. Wearable tech can predict heart attacks and track changes in respiration associated with COVID. Wireless hospital beds track biometrics and communicate with other devices (i.e., X-rays or blood-pressure monitors) to monitor a patient’s health and automatically make necessary adjustments.
But while the Internet of Medical Things (IoMT) is flourishing, it is facing an ever-present insidious threat: cybersecurity attacks that can disable essential systems, attack critical supplies, steal patient data, and lead to high costs for healthcare providers. COVID-19 has created new opportunities for cybercriminals to profit from attacks. I spoke to Sumit Sehgal, Strategic Product Marketing Director at Armis, to find out more.
The etiology of IoMT
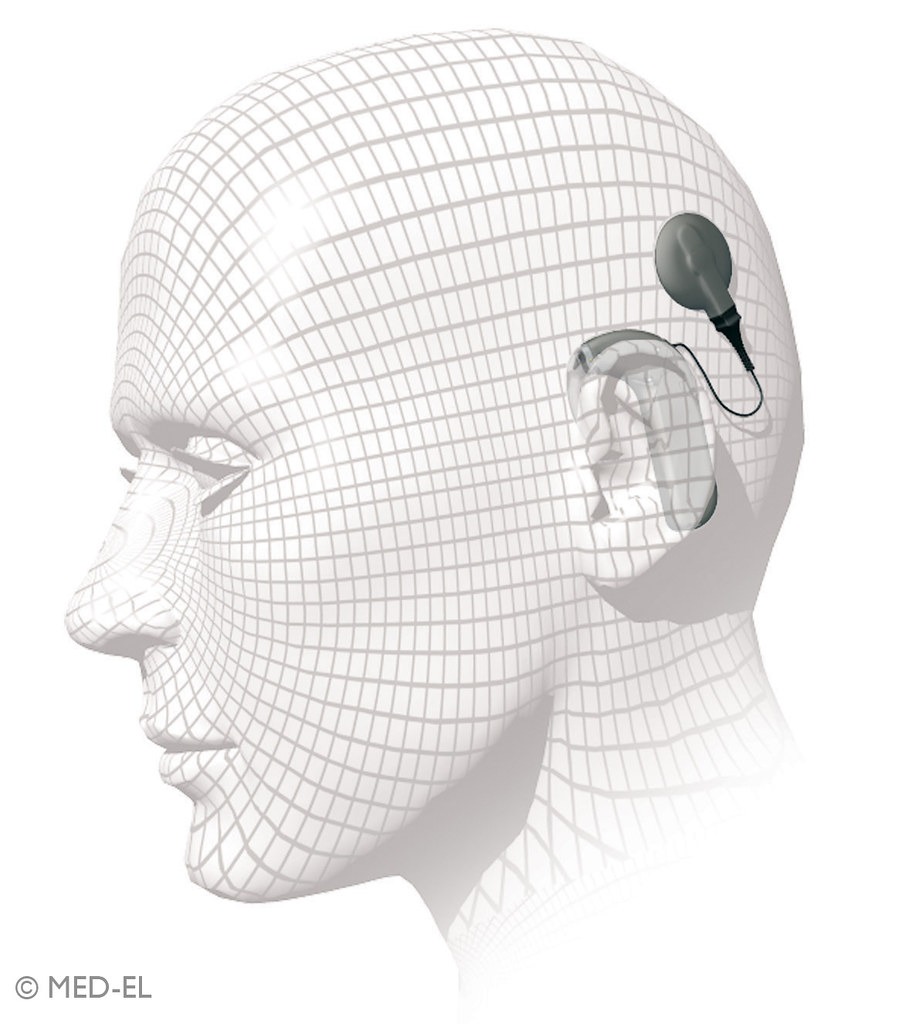
Fixed function devices and implantable IoT have existed in connected healthcare for well over a decade. For example, healthcare providers commissioned the first commercial cochlear implant in the 1980s.
However, since its inception, the Internet of Medical Things (aka IoMT) has been a compelling opportunity for cyberattacks. In 2017, The U.S. Food and Drug Administration (FDA) recalled almost half a million pacemakers due to cyber threat vulnerabilities. Researchers found that St. Jude Medical’s RF-enabled implantable cardiac pacemakers contained security vulnerabilities that, if exploited, could allow an unauthorized user to access a patient’s device using commercially available equipment. Hackers could use this access to modify programming commands to the implanted pacemaker, resulting in patient harm from rapid battery depletion or administration of inappropriate pacing.
The FDA has also revealed vulnerabilities in specific insulin pumps, where an unauthorized person could potentially connect wirelessly to a nearby MiniMed insulin pump with cybersecurity vulnerabilities. A hack could change the pump’s settings to either over-deliver insulin to a patient, leading to low blood sugar (hypoglycemia), or stop insulin delivery, leading to high blood sugar and diabetic ketoacidosis.
However, Sumit notes, the amount of effort needed to do so is exceptionally high.
“We see proof of concepts for these medical devices to be hacked. Can it be done at scale quickly? I would say it depends on the type of device and type of situation. The biggest change that has happened is the ability for raw compute power to figure out what the vulnerabilities are and to fingerprint that quickly and have an unauthenticated presence in that environment. The barrier to do that is very low, partly because of the distributed environment that we live in now.“
It is far easier to bring a hospital down by attacking the patient care ecosystem, including security cameras, lighting, vacuum tube systems, and monitors. Imagine an attack on just one elevator:
“If your hospital has 30 floors in a building, and the elevator control system goes down, it’s very difficult to move patients from surgery on the second floor to the ICU, which may be on the fifth floor. But it can cause chaos. And I think that’s [what] the industry is grappling with at this point.”
The last few years have cemented the efficacy of ransomware attacks via social phishing attacks via software, such as government municipalities disabled by crippling cyberattacks. Sumit explains, “We’re seeing a lot of changes occurring in the sense of purpose-built malware coming into specified devices or smart devices. We’re also seeing a diversion tactic where you create noise and distraction in one place while attacking elsewhere.”
The cost of security to innovation
Sumit speaks of an industry challenged by the pace of innovation vs. the relative costs of security: “Some of the newer devices are doing better in their approach to security management, because when you take a look at the device ecosystem, you have the large behemoths that have been around for 30, 40, 50 years, and at some point, you have to figure out where the money’s allocated to balance the innovation for newer tech and the legacy debt of products running 20 years past their expiry date. You have pretty much zero security for devices built about 10 years ago.“
However, new tech, especially the cloud-enabled tech, is, fortunately, leveraging the best security practices of the software development lifecycle. Sumit explains, “They’re architects of methodologies to help navigate not only just the data protection but identity and telemetry for behavior mapping because that’s kind of where the entire security industry is going with their approach on how to deal with this problem.”
Who is responsible for securing the Internet of Medical Things (IoMT)?
According to Sumit, it takes a village. At some point, the responsibility of securing device data sits on the organization that’s harvesting it to provide the service. But hospitals can only do so much, because if you put data on a poorly designed device, then that becomes a device manufacturer issue.
He explains that a convergence of security responsibility is coming together across multiple parties within IoMT and healthcare:

“It’s said that during the pandemic, health care went through eight to 10 years of innovation in a span of eight months. Ti. hat has essentially coalesced itself in a way that’s forcing them to think about security more in the lens of the patient. That’s what’s helping improve the relationships, because both sides of the equation understand the use cases better. So that’s helping with shared understanding from a device behavior perspective.”
He notes that in the last five years, hospitals, for example, have “shifted towards availability, integrity, things like the continuity of operations, and how to effectively design appropriate security architecture. It takes care of the data protection regulations automatically. Manufacturers created the whole ecosystem of the IoT medical devices to help drive visibility. But now the conversation is shifting to say, ‘Okay, we have enough decent visibility, we have enough of a profile behavior, let’s figure out how we can actually make that impactful where we can make decisions and take actions.’ Those are the pathways by which we’re seeing a lot of momentum.” As a result, Armis’ work is not only reactive but preventative.
“They’ve seen the havoc that attacks can have on the operation side of things, not just data. So at a board level, the industry has come together and said we can’t ignore this problem anymore.”
A proactive reaching out has also occurred in health areas, such as temporary hospital sites and the expansion of remote health services, such as telemedicine programs.
Who’s breaking into IoMT and healthcare?
There are two aims regarding hacking healthcare and the Internet of Medical Things (IoMT): data theft and disruption. Thefts of personally identifiable information, protected health information, patient and research data are commonly associated with nation-state threat actors who sell data and personal information to the highest bidder. Disruptive attacks are underpinned by efforts to cause affray but also lead to financial gain through ransomware.
According to Sumit, at the heart of a hospital is its role as a business enterprise. “Nation-state sponsored targeted attacks go after critical infrastructure to disrupt the supply chain, logistical processes and clinical workflows. Have they happened? Yes. Do they happen every day? Yes, those kinds of campaigns occur. However, we’ve come a long way, in intelligence matters, as well. So generally, it’s difficult for them to avoid detection.”
COVID-19 creates new attack vectors for enterprising cyber criminals
We’re currently in the midst of one of the largest vaccine rollouts in recent decades. Cybercriminals take advantage of any opportunity. COVID has resulted in fake testing clinics, fake vaccines and a plethora of COVID vaccination scams. Supply chain attacks have seen attackers target the transportation and cold chain storage of vaccines. In April, IBM Security X-Force released research of phishing emails. Hackers targeted 44 companies in the COVID-19 vaccine supply chain across 14 countries.
According to Sumit, epidemiological research into COVID-19 is also prone to attack. Although released, vaccines are still undergoing ongoing research trials. Insights into the efficacy of vaccines or changes in the vaccine formulas are valuable. They can enable pharmaceutical companies to gain business advantages. There’s also incentivization from the hackers to say, “Hey, if I can get a formula, I can sell that downstream to have manufacturing occur by other parties.”
What’s the next cybersecurity challenge for IoMT?
Healthcare organizations have been swift to adopt cloud-enabled IoMT, meaning its distributed environment makes it harder to secure. Sumit believes the next threats will occur in implantable technology, nanotechnology, AR, and voice tech. “Security is not featured from an architecture perspective. We need to focus on figuring it out. There’s the triad of security: confidentiality, integrity, availability. We need to understand what integrity-based attacks will look like. We need to understand how they will impact connected devices and the way they function.”