
As we head into 2019, the security gaps of IoT devices show no sign of closure. Industry players are happy to talk about security in a broad, non-committal sense. Few, however, are willing to discuss common sense security arrangements despite a three-time increase in IoT malware variants during 2018.
Currently, all major IoT platforms have their own set of security standards which they internally follow. Apple’s HomeKit and Google’s Nest are among the dozen or so smart home platforms that don’t really communicate with each other. While device manufacturers join one or the other default standards, as an IoT consumer you have no choice in this matter.
Current Industry Initiatives
Even though IoT devices and platforms have compatibility issues, some progress in standardization is underway. The Open Connectivity Foundation (OCF) today boasts big names including Microsoft, Samsung, LG, Electrolux and Cisco. At the moment, OCF supports 2426 devices. That’s definitely a huge number.

The challenge, however, is far from over. At its root lies the role of Microsoft as the founder of OCF, which discourages many others from joining this elite group. Instead of being “open,” OCF feels like an exclusive golf club where you have to buy your way up with Gold, Platinum and Diamond memberships. If OCF should then become the default torchbearer for IoT standards, would it not make the IoT customers irrelevant? This point is open to debate.
What’s Next? “Trustable Technology Mark”
Against this backdrop of emerging industry monopolies, a few promising startups are arriving with their own security certifications. One such sticker is the “Trustable Technology Mark” (TTM) recently launched by ThingsCon, a European non-profit organization along with the Mozilla Foundation. Their principle mission is to “foster human-centric and responsible Internet of Things.”
As new as it sounds, there are practical benefits of non-profit organizations like these creating the security standards of tomorrow. If device manufacturers aspire to having independent certifications in IoT security, consumers will benefit from the measure.
Remember the use of “CE” marking in electronics which only began in the 1980s. Today, the mark has not only become mainstream but is mandatory for many kinds of electronics products. Clearly, Trustable Technology Mark will have potential from the day consumers demand that IoT players start conforming. Right now it is too early though.

More Details
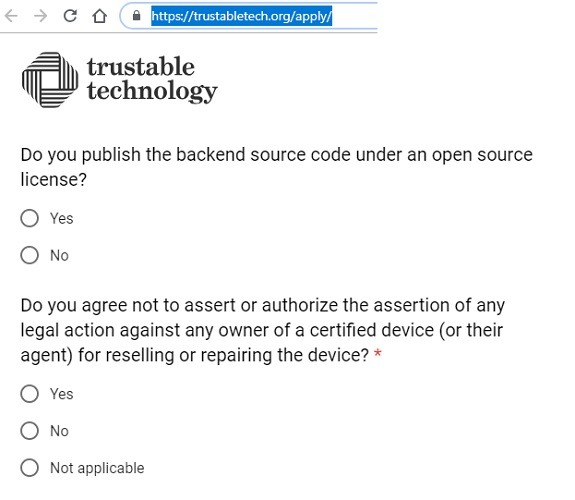
How exactly does this new security certification benefit the IoT consumer? Basically, a device manufacturer has to apply for self-certification at this link. It contains an honest self-assessment of the company’s security and privacy initiatives based on fifty questions. ThingsCon reviews the application on a case-by-case basis and awards a certification in the end. The assessment forms are available on their website. This is what I call transparency!
Conclusion
The message from IoT industry players is quite simple: “If you’re not exclusively buying our products, we aren’t interested in providing you security everywhere.”
Trust in IoT products will only begin when big IoT players get off their dizzying heights and conform to uniform standards. Governments can play a leading role in ushering and enforcing independent IoT standards rather than playing nice with corporations.
Certifications like Trustable Technology Mark will go a long way in building consumer trust in their IoT purchases. However, we are in a very, very early stage, and so far, only two IoT devices have conformed to the new standards. This seems to be the Linux of our age and it remains to be seen whether this customer-centric initiative has any real takers.









