Buying new smart technology is exciting! There’s nothing more gratifying than ripping the box open and adding the new smart device to your network. Do you ever consider what this does for your personal security? Are you inadvertently putting yourself at risk? To optimize your network security, it’s best to segregate your network for IoT devices.
Why Segregate my Network?
Security is always at the forefront of smart home technology concerns. Along with all of the benefits that these awesome devices provide, they also open up a new window into your home. Many people have become able to come to grips the fact that device manufacturers are collecting your data. Are you concerned about unwelcome intruders making their way into your network as well?

It October 2019, Kapersky Labs released a report on the detection of 100 million malware attacks on IoT devices in H1 of 2019 – seven times more than the previous year. This is a frightening statistic. Employing a network segregation strategy is the absolute best way to keep this malware from infiltrating the rest of your network.
How Do I Segregate my Network?
Setting up segregation is easier than you may think. It’s worth your time and effort. Here are the steps it takes to make this happen.
Verifying Router Compatibility

First, figure out if the router that you are currently using is able to support multiple SSIDs and multiple networks. Many of even the most cost-effective consumer-grade wireless devices at least offer a “guest” network option that can be repurposed for your IoT network. The more feature-rich wireless routers offer the capability of creating as many SSIDs or networks as you need, giving you more flexibility.
Creating An Alternate SSID
Create an SSID meant only for your IoT devices. Give this network an obvious label so that you know you are reaching the right network every time. To prevent devices that are not meant for this network from connecting, be sure to lock this down with a unique passphrase. In more extreme cases, you can also consider not broadcasting this specific SSID.
Establishing a Unique Network
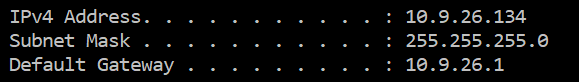
With this unique SSID should come a unique network. To make your networks easily distinguishable, consider using a subnet within a different private class. Using unique subnets ensures the separation of data, making configuring firewall rules easier.
Forbid Interaction Between Networks
Once your separate networks have been established with unique SSIDs and different IP schemes, it’s important to check firewall rules to make sure that the two networks are not allowed to interact. Depending on the situation, you may want to allow one-way traffic from the main network to your IoT network. In other cases, you may want to consider creating rules that deny all traffic between the networks.
Conclusion
As you add more smart devices to your network, you are widening your surface area of attack. When you segregate your network for IoT devices, you are preventing threats from making it from these devices onto your central network.
What other steps have you taken to protect your network from IoT device-based malware? Comment below to let us know!