In any situation dealing with technology, security is paramount. Because of the shifting threats and needs of both businesses and end users, different security paradigms come and go.
As software and companies become more complex, so do their security needs. The larger the organization, the more these issues matter. That’s one of the problems that Zero Trust architecture is meant to solve.
Introducing Zero Trust Architecture
You may be familiar with the term “trust but verify.” This is a concept many security methods are built on. In some cases it can work well, but when security is crucial, this may not be enough.

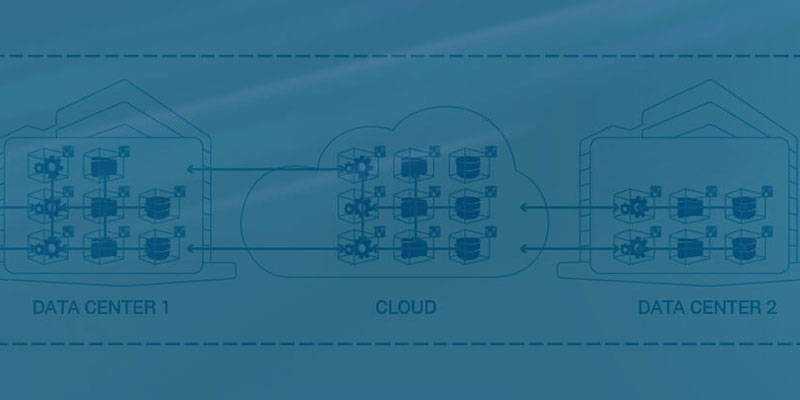
The central concept of Zero Trust architecture can be summed up as “never trust, always verify.” This means elements that would be inherently trusted in other security methods, like internal servers and employees’ devices, aren’t trusted. This can reduce your risk against external threats, since even if they appear to be internal, they won’t be trusted.
Why Is Zero Trust Architecture Important for IoT?
IoT is one area where Zero Trust may be particularly useful. More devices means more potential attack vectors, and we’ve already seen IoT devices taken over and used in larger hacks. If you trust IoT devices on premises, an attacker could use them to target other devices from the inside.
Implementing Zero Trust Architecture
A Zero Trust system can be more difficult to implement with IoT. These devices are meant to be autonomous, so it can be tricky to constantly verify them. One way to handle it is to harden your internal devices as if they were exposed to the internet to keep them clear of vulnerabilities.
Zero Trust should also cover all devices in a certain business area. That means that bring-your-own-device and other similar schemes should be discouraged. If you can’t completely control a device, it shouldn’t be able to access anything.
Monitoring is also important here. If any unusual traffic or device activity is detected, this raises major flags. Fortunately, with a Zero Trust system, it should be easier to detect which user or device is the cause.
You Don’t Need to Go All in at Once
Zero Trust architecture may seem like an all-or-nothing proposition, but that’s not the case. Implementing Zero Trust can be tricky, but you don’t have to do it all at once. This can make adoption easier, plus, you can determine whether it works for you.

You can start by implementing Zero Trust in one aspect of your business, particularly one that you’d like to make more secure. This may turn out to be all you need, and you can use other security concepts in other areas of your business.
Conclusion
Zero Trust architecture might be popular now, but that doesn’t necessarily mean it’s for you. If you find your needs are met by your current security, you may not want to switch. That said, keep in mind that waiting until you have a security breach isn’t an ideal way to evaluate your security.
It helps to consider what type of threats you have to worry about. If you aren’t sure, take a look at our list of common security threats.









